Bitwarden Password Manager Hacked: Popular Tool Downloaded Malicious Code 78,000 Times
Hackers compromised Bitwarden's command-line password manager tool, stealing sensitive data from users who downloaded the infected version. The malicious code grabbed passwords, cryptocurrency wallet keys, and other private information from roughly 78,000 weekly downloads.
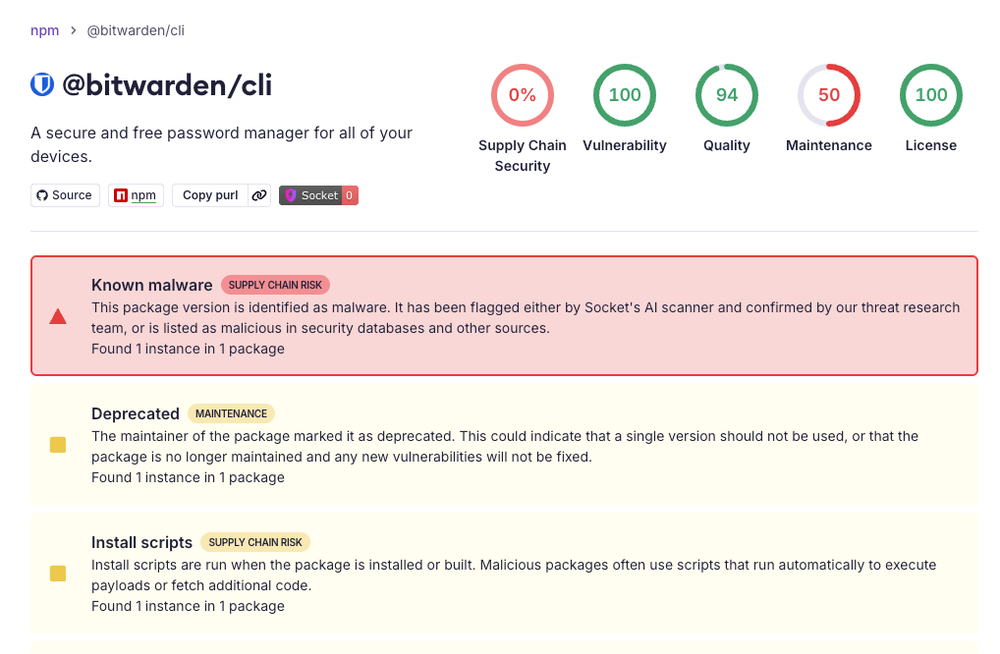
Cybercriminals successfully hacked Bitwarden's command-line interface (CLI) tool, a technical version of the popular password manager used by developers and tech-savvy users. The attack affected version 2026.4.0 of the @bitwarden/cli package.
The hackers used a technique called a supply chain attack, where they corrupted the software before users downloaded it. They specifically targeted GitHub Actions, the system developers use to automatically build and distribute software.
Once installed, the malicious code stole a wide range of sensitive information from victims' computers. This included GitHub and npm tokens, SSH keys, environment files, shell command history, and cryptocurrency wallet information.
Security researcher Adnan Khan noted this represents the first known compromise of a package using npm's trusted publishing mechanism. This system was designed to be more secure by eliminating long-lived security tokens.
The attack is part of a larger campaign by a group called Checkmarx TeamPCP, which has been targeting software supply chains. JFrog Security identified the compromise and warned that it affects users with 78,000 weekly downloads.
If you use Bitwarden's technical tools, your passwords and crypto wallet keys might be stolen. This attack shows hackers can infiltrate even security companies meant to protect your data, putting your money and accounts at risk.
Users should check if they installed the compromised version and change all affected passwords and tokens.
Was this article helpful?
0 people found this helpful