Firefox Bug Lets Websites Track Users Across Tor and Private Browsing Sessions
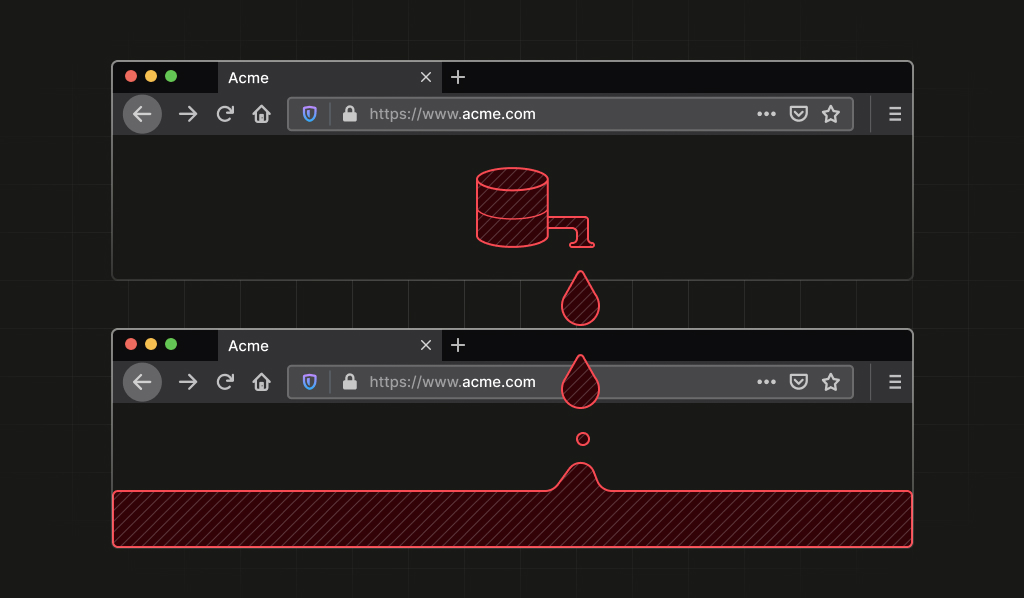
Security researchers discovered a bug in Firefox that creates a permanent identifier, allowing websites to track users even when they use Tor browser or private browsing mode. The identifier persists after closing private windows as long as Firefox is still running.
Security company Fingerprint found a vulnerability in Firefox that undermines user privacy by creating stable identifiers that persist across supposedly anonymous browsing sessions.
The bug affects Firefox's private browsing mode and the Tor browser, which is built on Firefox. Even after users close all private windows, the identifier remains active as long as the Firefox process keeps running in the background.
This means websites can recognize return visits in what appears to be a completely fresh private session. Users who rely on these tools for sensitive browsing - from journalists protecting sources to people in countries with internet censorship - could be tracked without knowing it.
The vulnerability is part of a broader tracking technique called "scheme flooding" that uses information about installed apps to create permanent identifiers. This method works even when users switch browsers, use VPN services, or browse in incognito mode.
Fingerprint reported the bug to Mozilla, though the timeline for a fix remains unclear. The discovery highlights ongoing challenges in maintaining true anonymity online, even with tools specifically designed for privacy protection.
This bug breaks the privacy protection that millions rely on when using Tor or private browsing. Websites can secretly track your activity across what you thought were separate, anonymous sessions, potentially exposing sensitive browsing habits.
Mozilla will need to release a Firefox update to fix the vulnerability. Users should restart Firefox completely between private browsing sessions as a temporary workaround.
Was this article helpful?
0 people found this helpful